Are you able to monitor your inside SSL certificates? This was a query we often heard from our shoppers. Many organizations maintain their providers (net, database, and so forth.) inaccessible on the general public web, for safety, compliance, price, and different causes. At TrackSSL, we initially provided public SSL/TLS certificates monitoring, however we regularly obtained requests from clients for personal SSL certificates monitoring. Thus, we wanted to discover a technique to monitor certificates used on servers that aren’t usually accessible from the Web.
On this article, we share our journey of growing a distant certificates monitoring service utilizing an agent that runs on a company’s personal community. We share the necessities we outlined, the structure we chosen, and the answer we carried out.
Let’s dive in.
Technical Necessities
Our aim was to construct a monitoring system that may monitor certificates on inside networks and we selected the next necessities:
1. Light-weight and Environment friendly
The agent we used needed to be small and light-weight. It ought to use minimal information heart sources. It has to run seamlessly with out affecting the efficiency of different techniques. Scheduling automation also needs to be in-built.
2. Easy Runtime
The agent needs to be versatile, operating both a containerized software or a single executable. It ought to be capable to run on a number of platforms together with Mac, Linux, and Home windows.
3. Assist for A number of Brokers
It ought to accommodate distinct personal community segments throughout a company. The agent ought to be capable to be deployed throughout the segments. This ensures complete monitoring all through your complete community infrastructure and even in several workplaces, buildings, or places.
4. Delegated Processing
The agent ought to solely deal with important duties throughout the personal community. Extra intensive processing might be delegated to the prevailing cloud-hosted API and dashboard. This strategy will lower the load on inside techniques and maintain the method straightforward to keep up.
5. Complete Certificates Assist
The agent ought to help self-signed certificates and certificates issued by standard public certification authorities. Moreover, it screens any sort of TLS certificates, together with HTTP and LDAP.
6. Open Supply Code
It’ll have a publicly out there code. This manner, any group can evaluation and confirm its safety and reliability. This transparency fosters belief and confidence in our answer.
Right here’s what we determined to construct based mostly on the necessities we listed.
The Structure Behind the TLS/SSL Certificates Monitoring Agent
Based mostly on the necessities we outlined, we developed the structure of our TLS/SSL monitoring agent. Right here’s an in depth have a look at it:
Growth and Language Selection
The agent is developed in Ruby, which is in line with the remainder of TrackSSL’s infrastructure. This determination leverages our crew’s experience, guaranteeing easy manufacturing and upkeep. Ruby is called a versatile scripting language used for all kinds of duties. Though it might need decreased efficiency in comparison with lower-level languages, high-volume efficiency was not a difficulty for this use case.
Docker Containerization
The agent is containerized utilizing Docker, offering a strong and industry-standard deployment methodology. Docker’s widespread use in enterprises ensures dependable and constant efficiency throughout numerous environments.
Configuration
The configuration included:
1. Easy Configuration File
Configuration is managed by an simply editable textual content file. It’s accessible throughout platforms with minimal technical data.
2. Public Token and Non-public API Key
Firstly, the person creates an agent within the TrackSSL dashboard. Then, a public token and a personal API key are generated. The general public token is just a singular identifier used to affiliate the certificates on that inside community with certificates the person has beforehand outlined contained in the TrackSSL dashboard. The personal API key’s the securely generated secret used to authenticate to the API. This token should be saved personal.
3. Straightforward Setup
Customers place the configuration file in the identical listing because the Docker container. The agent then robotically pulls the required settings and makes API calls again to the cloud-hosted course of utilizing the general public token and personal API key.
Scheduling and Execution
Constructed-In Scheduling
The agent makes use of a “rufus-scheduler” to schedule certificates checks each 4 hours. This eliminates the necessity for cron jobs or additional system configuration. It is a light-weight gem that’s generally utilized in Ruby purposes to schedule duties utilizing commonplace cron syntax. It’s multi-threaded and has been well-maintained for greater than a decade, making it a great candidate.
Asynchronous Execution
With “sucker-punch”, the agent fetches certificates in parallel. Thus it performs high-volume checks without having a further daemon like Sidekiq. That is one other gem that’s extensively used and well-maintained, having been in lively service for greater than 12 years. A gem that’s saved up-to-date and maintained is crucial, particularly for software program that may run unattended on numerous deployments across the globe.
The Technique of Checking Certificates
When checking certificates, we ensured the next:
API Name
The agent calls the TrackSSL API to retrieve the listing of certificates each 4 hours. Utilizing the personal API key, the agent fetches the listing of certificates which were beforehand assigned to its distinctive identifier, the general public token.
Certificates Retrieval
The agent connects to specified servers and ports on the native community. That is the important thing step that’s solely attainable on the native community. As a result of these can usually be non-routable IPs or inside hostnames that don’t resolve publicly, it’s important this step runs contained in the native community. The agent retrieves certificates based mostly on hostnames or IP addresses and doesn’t entry some other information. As soon as it connects to the port and fetches the certificates, the connection is closed. This maintains privateness and safety throughout the personal community.
Safety Issues
The agent strictly retrieves certificates with out making HTTP connections. So, it adheres to high-security requirements and fosters buyer belief. As a result of the agent is open supply, customers can see that no different information is accessed by the agent.
Integrating With TrackSSL API
When integrating with the TrackSSL API, we thought of the next two components:
1. Certificates Dealing with
The agent posts the retrieved certificates to the TrackSSL API. Then they’re processed and dealt with like all public certificates. As a result of detailed evaluation of the certificates doesn’t occur contained in the agent, we are able to restrict the floor space of the deployed brokers.
2. Centralized Notifications
All notifications are managed within the cloud, so the purchasers don’t deal with e mail notifications, SMTP administration, or certificates parsing.
Our answer is a daemon course of written in Ruby. It makes use of OpenSSL for certificates dealing with. OpenSSL gives simplicity, a small footprint, and dependable encryption. These are its core strengths in certificates administration.
We plan to scale as much as deal with extra certificates and improve error and exception dealing with.
Person’s Perspective: The Launching Course of
When launching, we saved our customers in thoughts. So, we thought of the next:
1. Creating an Agent Occasion
Customers begin by creating an agent of their TrackSSL account. You’ll be able to title the agent after your inside community or select any memorable title. Every inside community requires its personal agent.
You’ll be able to create many brokers in your separate networks, subnets, or VPCs. Every one might be answerable for its set of certificates. Copy the generated token in your agent, known as TRACKSSL_AGENT_TOKEN.
2. Assign Domains to the Agent
Subsequent, a person wants so as to add a site representing a hostname or IP deal with that serves because the endpoint for an SSL/TLS certificates. Navigate to the “Domains” part on the left to assign domains in your inside agent. Then choose the area and select the corresponding agent.
3. Generate an API Token
Subsequent, create an API token in your agent to make use of. One API token suffices whatever the variety of brokers. Nevertheless, you possibly can create a number of tokens and revoke them as wanted.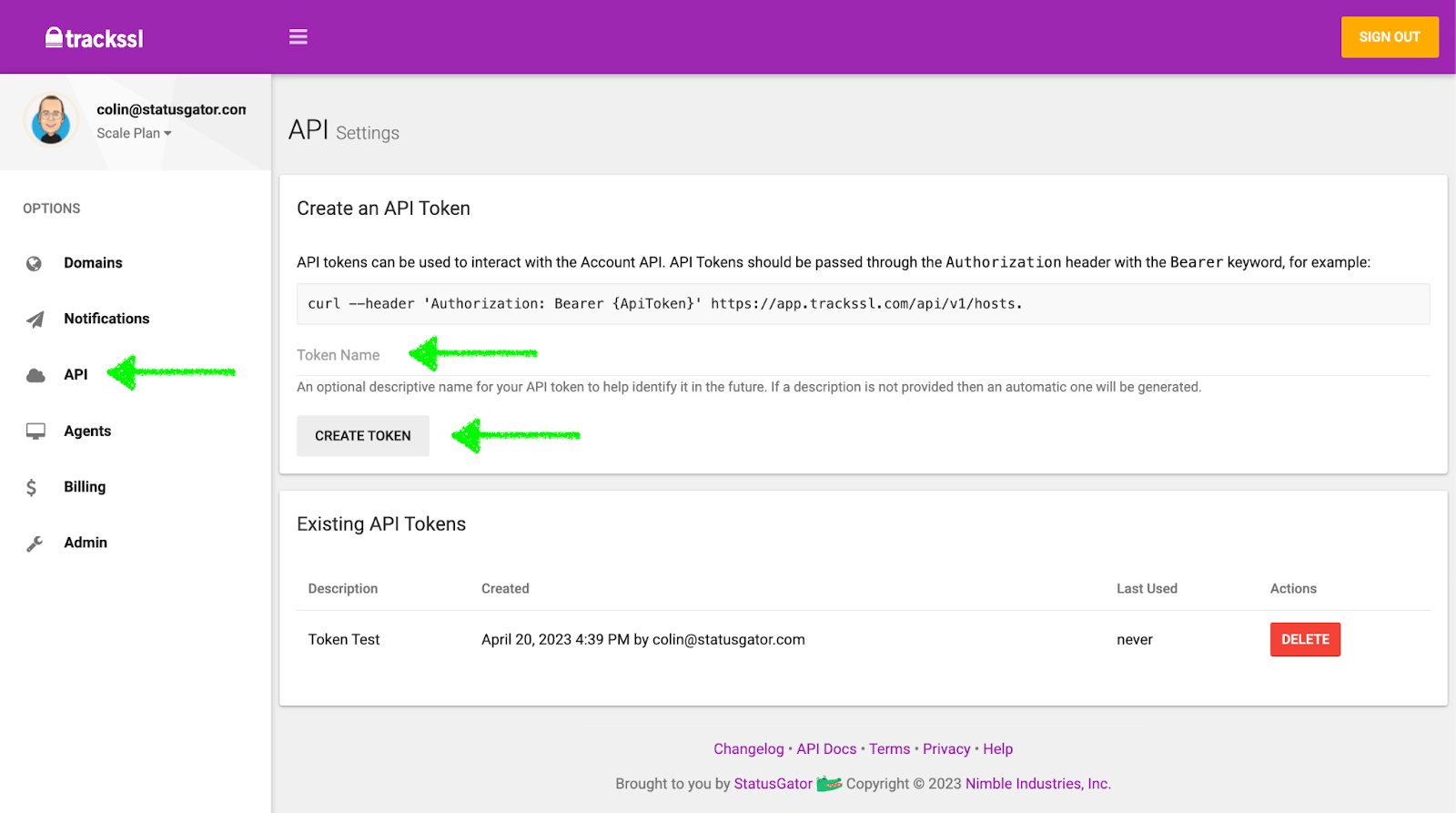
- The generated API token is known as
TRACKSSL_AUTH_TOKEN. - Place each
TRACKSSL_AUTH_TOKENandTRACKSSL_AGENT_TOKENright into a file namedatmosphere.txt, formatted as follows:
TRACKSSL_AUTH_TOKEN=your_api_token_here
TRACKSSL_AGENT_TOKEN=your_agent_token_here4. Pull and Run the Docker Container
Obtain and run the Docker container with the next instructions:
$ docker pull ghcr.io/trackssl/trackssl-agent:newest
$ docker run -d --env-file ./atmosphere.txt --name trackssl-agent ghcr.io/trackssl/trackssl-agentAs soon as the agent occasion is launched on an area community, it operates on a schedule each 4 hours. The agent will:
- Make an API name to the platform’s cloud-hosted dashboard.
- Fetch the listing of certificates it screens.
- Retrieve every certificates out of your native community.
- Push the certificates to TrackSSL within the cloud for notification and monitoring.
By following these steps, we ensured a seamless launching expertise.
Conclusion
Our monitoring agent addresses the necessity to monitor inside TLS/SSL certificates. It helps a variety of certificates and gives versatile deployment choices.
One enchancment we plan to make is to simplify the set up course of additional. Certainly one of our core assumptions is that Docker is extensively put in throughout the enterprise and out there in most environments. Nevertheless, this turned out to not be true. Many TrackSSL clients don’t have Docker and like a single runtime executable they’ll use on any platform. This iteration is within the works.
Tell us what you consider our strategy to inside SSL certificates monitoring within the feedback under. What would you do otherwise?
