In at present’s dynamic enterprise surroundings, cloud computing has change into a vital enabler, providing enterprises unmatched scalability, flexibility, and cost-efficiency. Amazon Net Companies (AWS), a number one cloud service supplier, has reworked how organizations handle their IT infrastructures and functions. With AWS Digital Non-public Clouds (VPCs), companies can set up safe, remoted environments throughout the cloud, replicating the capabilities of conventional on-premises networks. Nonetheless, regardless of the clear advantages of cloud adoption, bridging the hole between on-premises networks and AWS VPCs might be difficult, significantly when coping with overlapping IP addresses. Conditions usually come up the place on-premises networks and AWS cloud environments unintentionally use the identical non-public IP addresses, obstructing communication and knowledge change throughout the VPN tunnel.
This text addresses this particular concern and explores an progressive answer for establishing safe connectivity between overlapping on-premises networks and AWS VPCs. Leveraging AWS site-to-site VPN, the normal technique for connecting on-premises environments and VPCs, enterprises often face obstacles when managing conflicting IP addresses. Mergers, acquisitions, and different networking complexities additional complicate the scenario, making easy decision tough.
Pilot VPC and Superior Twice NAT Expertise
To handle these challenges, this text introduces the idea of Pilot VPC and Superior Twice NAT know-how. By strategically implementing digital routers and Clover community handle translation, enterprises can successfully navigate overlapping IP handle points, guaranteeing seamless communication between on-premises networks and AWS VPCs.
The usage of these superior applied sciences not solely resolves the overlapping IP handle downside but in addition enhances community safety, knowledge privateness, and total operational effectivity. Within the following sections, we’ll discover the technical particulars of Pilot VPC and Superior Twice NAT know-how, highlighting their position in creating a sturdy and safe community infrastructure. By offering sensible insights and real-world examples, this text goals to equip companies with the information and instruments wanted to beat the complexities of integrating on-premises networks and AWS VPCs, finally fostering a seamless, hybrid cloud surroundings.
VPN Overlapping Community Points
Within the above diagram, we are able to see two distinct websites: the on-premise community and the AWS VPC (Digital Non-public Cloud), interconnected by way of a VPN (Digital Non-public Community) tunnel. This connection is established by way of the shopper gateway and the AWS VPN Gateway. Notably, each the on-premise community and the AWS VPC make use of the IP handle vary 10.0.1.0/24 for his or her respective inner networks.
Allow us to take into account a state of affairs the place communication is required between an on-premise Host (with IP handle 10.0.1.7) and an EC2 occasion (with IP handle 10.0.1.8) throughout the AWS VPC. On this scenario, the on-premise Host operates underneath the idea that each one IP addresses throughout the 10.0.1.0/24 vary belong to its native community. Consequently, when the on-premise Host makes an attempt to transmit a packet destined for 10.0.1.8, it is not going to direct the packet in the direction of the shopper gateway gadget.
Likewise, an identical predicament arises for an EC2 occasion throughout the AWS VPC. Assuming the EC2 occasion is configured with the IP handle 10.0.1.8, it additionally perceives the vary 10.0.1.0/24 as a part of its native community throughout the AWS VPC. Consequently, when the EC2 occasion makes an attempt to dispatch a packet to the IP handle 10.0.1.7, it’s going to route the packet inside its native community as an alternative of directing it to the VPN Gateway. This example presents a problem for the reason that packets will not be being routed to the VPN Gateways. Consequently, the VPN gateways are unable to ahead these packets by way of the VPN tunnel to the respective reverse aspect. In consequence, because of the overlapping networks, neither aspect is ready to set up a reference to the opposite, resulting in a communication failure between the on-premise Host and the EC2 occasion throughout the AWS VPC.
The Proposed Resolution for VPN Overlapping Networks
A transit gateway (TGW) is a central cloud router that allows you to join your digital non-public clouds (VPCs) and on-premises networks utilizing a hub-and-spoke mannequin. It combines attachment domains and routing domains to present you completely different choices for routing, just like VRF-style routing. The answer to the issue is to make every host consider that the opposite host is on a separate community. This fashion, when a packet must be despatched over the VPN tunnel, it goes to the router first.
Configure Your Community Utilizing a Transit Gateway
There are two methods to configure your community utilizing a transit gateway to facilitate options:
- The primary answer entails supply and vacation spot NAT configuration on equipment/Linux situations in Pilot VPCs. (Use this answer if a single VPC is overlapping with the on-premises community.)
- The second answer entails a NAT configuration on each on-premise buyer gateway units. (Use this answer if a number of VPCs are overlapping with the on-premises community.)
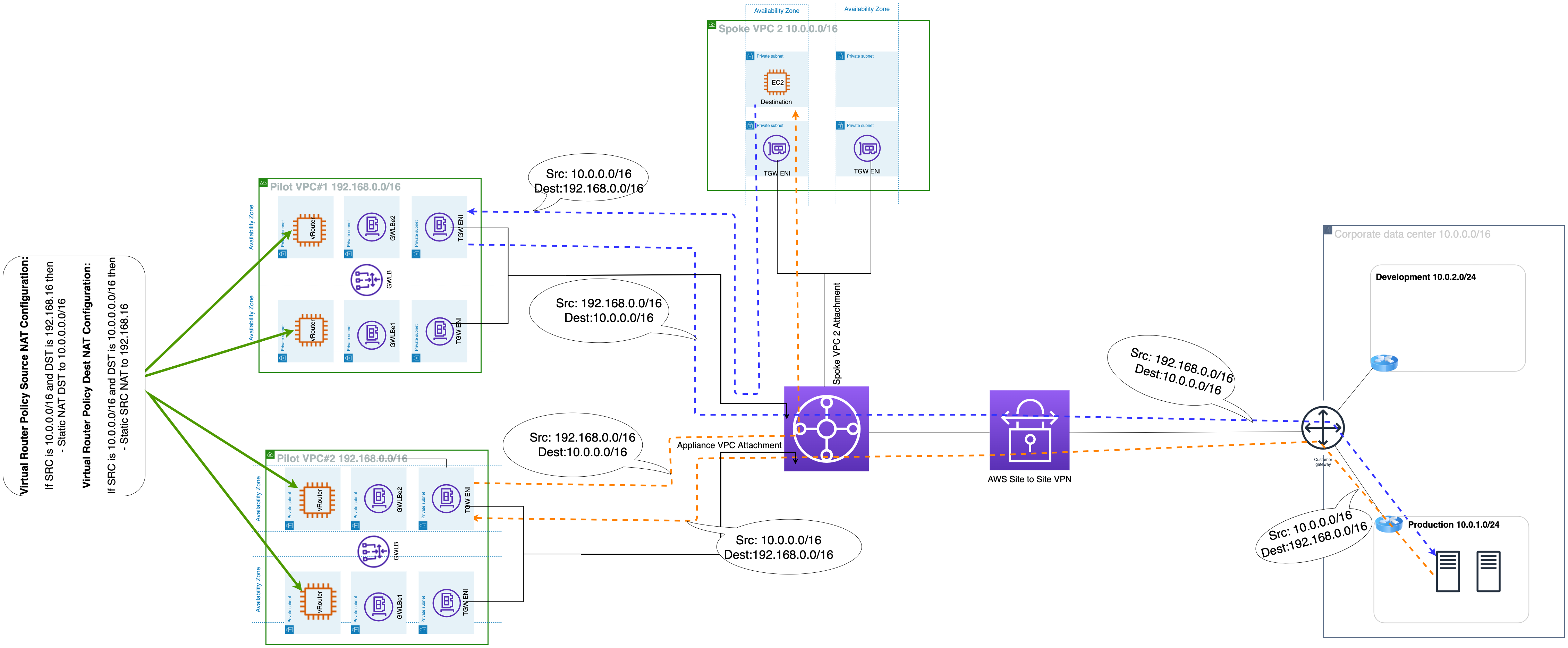
Resolution #1: Supply and Vacation spot NAT in Pilot VPCs
The answer requires two pilot VPCs the place we launch two digital home equipment (or Linux situations) in every VPC in two completely different availability zones (AZs) to supply excessive availability. The 2 VPCs could have the very same configuration, together with IP CIDR. The thought is to make use of two completely different TGW attachments and two TGW route tables to supply separate ingress and egress paths between the on-premise community and the precise buyer VPC. We’ll use the equipment’s site visitors management coverage motion to do SNAT and DNAT. This will likely be a stateless NAT configuration on these home equipment. Site visitors Management NAT motion permits us to carry out NAT with out the overhead of conntrack, thus giving us the choice to NAT giant numbers of circulation and addresses.
We configure a NATing coverage on home equipment in a manner that the ingress filter interprets vacation spot addresses; i.e., carry out DNAT. The egress filter interprets supply addresses; i.e., carry out SNAT. Filters configured on the equipment permit for environment friendly lookups of numerous stateless NAT.
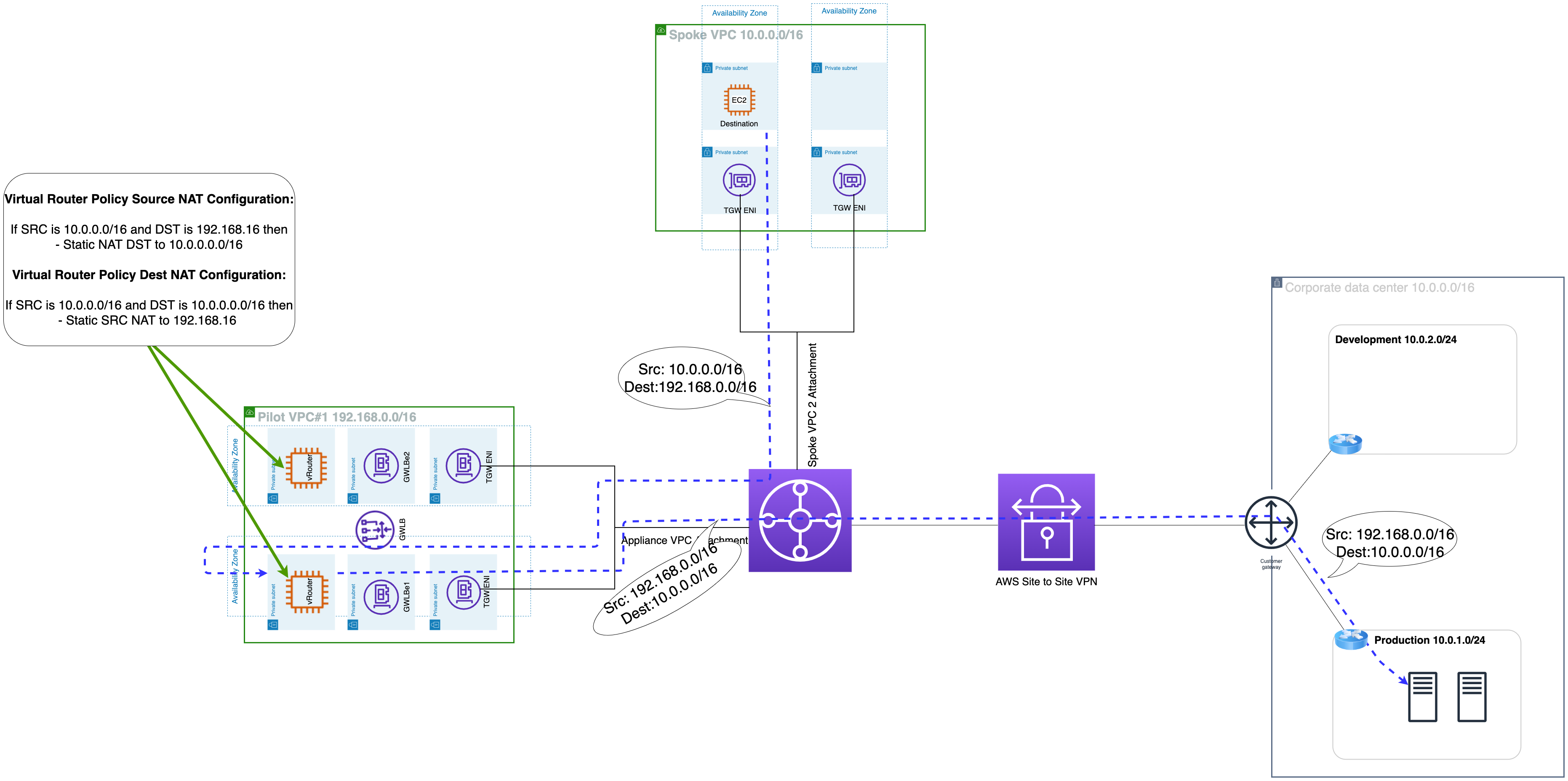
Ahead Site visitors Circulation
On-premise 10.0.0.0/16 → tgw-rtb-vpn → tgw-attach-Pilot#1 → NAT occasion in Pilot VPC#1 [NAT translation SNAT and DNAT] src 192.168.0.0/16 dst 10.0.0.0/16 → tgw-rtb-Pilot#1 → tgw-att-Dest VPC → VPC Blue 10.0.0.0/16
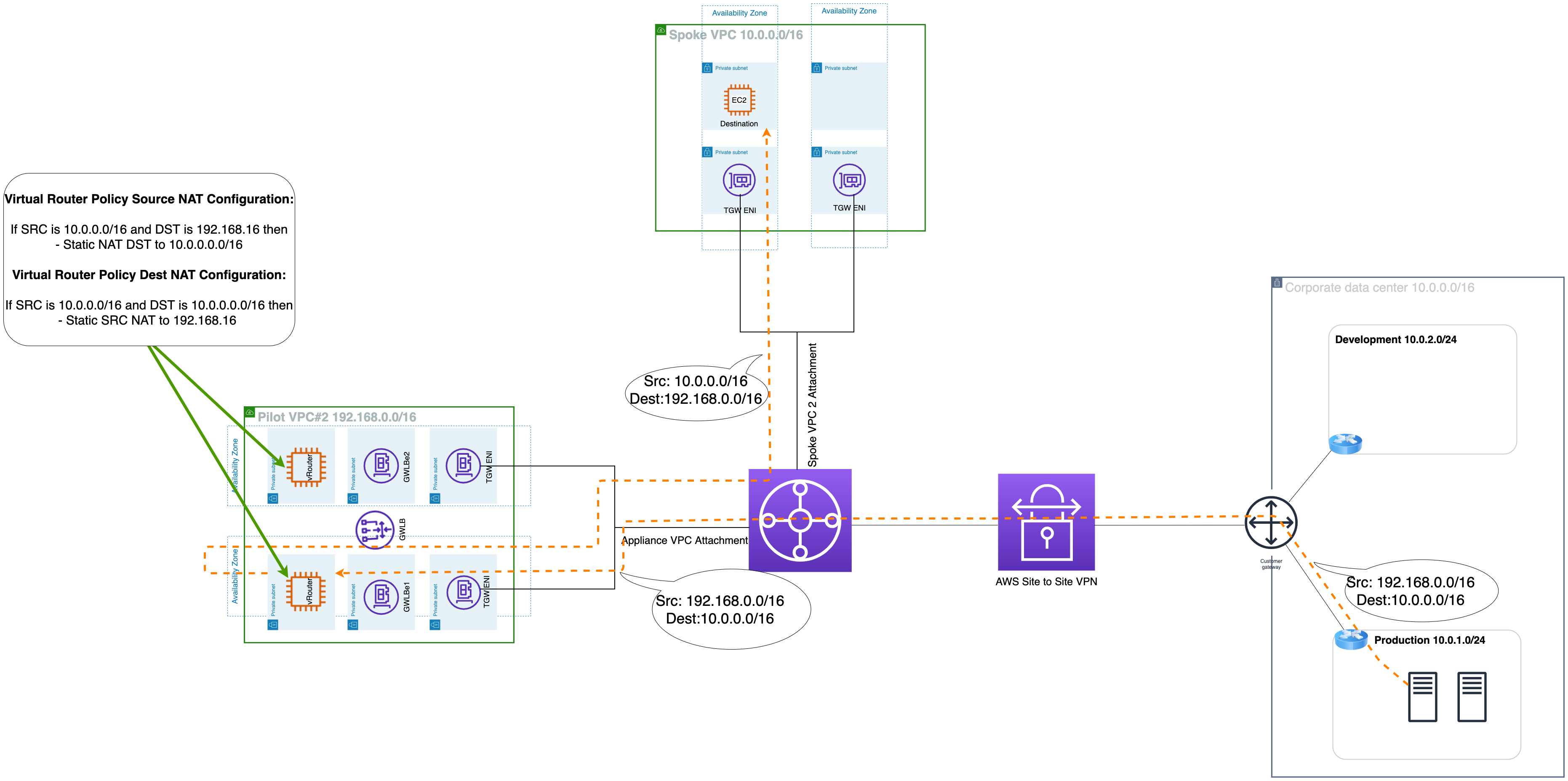
Equally, Return Site visitors Circulation
Dest VPC 10.0.0.0/16 → tgw-rtb-dest vpc → tgw-attach-pilot#2 → NAT occasion in pilot VPC#2 [NAT translation SNAT and DNAT] src 192.168.0.0/16 dst 10.0.0.0/16 → tgw-rtb-pilot vpc#2 → tgw-att-vpn → On-premise 10.0.0.0/16
The bi-directional site visitors circulation might be seen within the following determine:
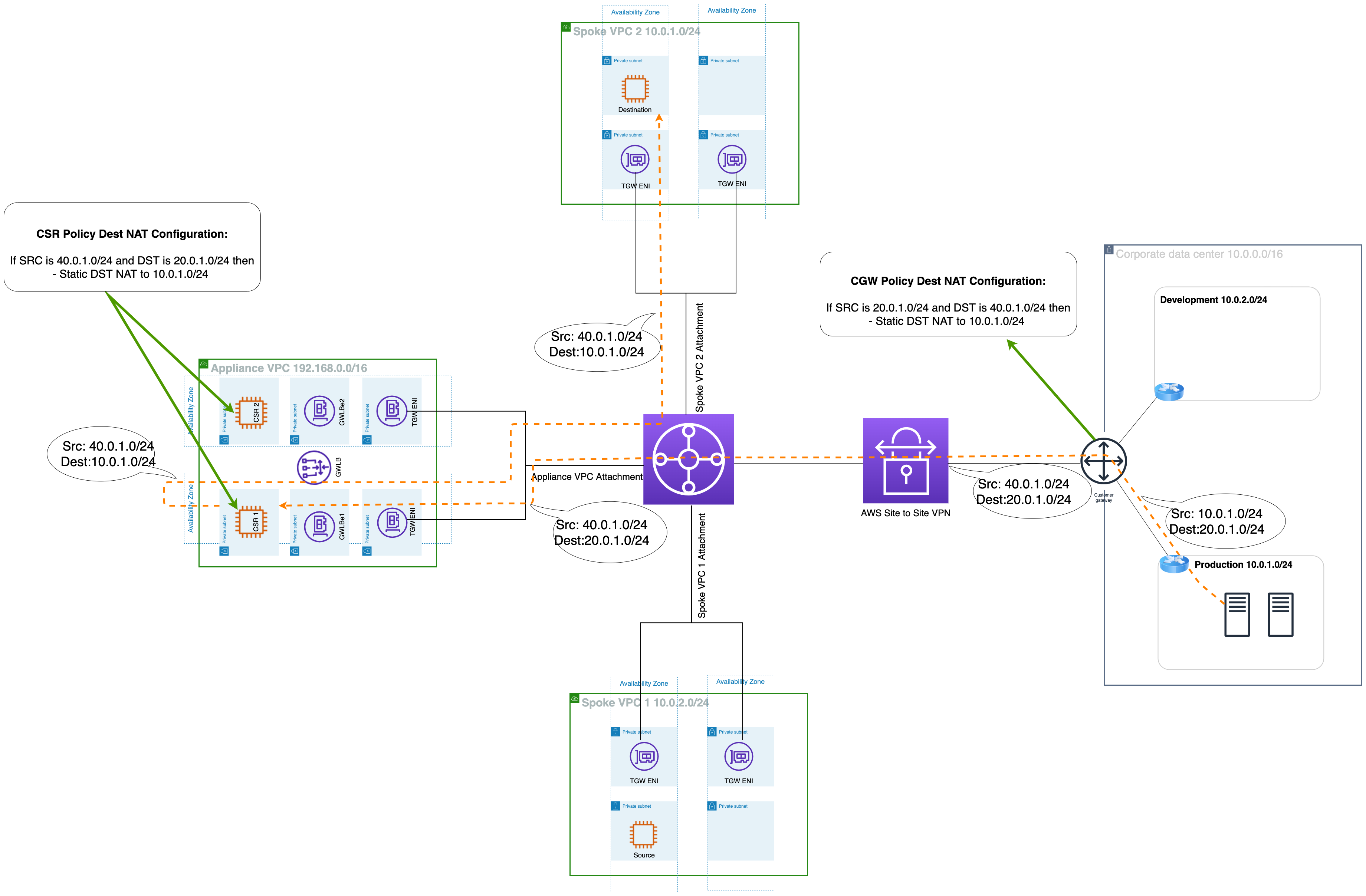
Resolution #2: Coverage NAT on Each Sides
This answer entails utilizing Coverage NAT on each on-premise buyer gateway and digital routers in AWS VPC to map their inner community when connecting to the distant community. On-premise buyer gateway’s Coverage NAT configuration will match packets with a Supply IP of 10.0.1.0/24 (On-premise’s precise community) and a Vacation spot IP of 20.0.1.0/24 (VPC’s masked community), and translate the Supply IP to the 40.0.1.0/24 community (On-premise community). Digital Router’s Coverage NAT configuration will match packets with a Supply IP of 10.0.1.0/24 (VPC’s precise community) and a Vacation spot IP of 40.0.1.0/24 (on-premises masked community), and translate the Supply IP to the 20.2.2.0/24 community (VPC’s masked community).
On this manner, on-premise CGW is masking the on-premise 10.0.1.0/24 community as 40.0.1.0/24, and the Digital router is masking the VPC 10.0.0.0/24 community as 20.0.1.0/24.
On-premise 10.0.0.0/16 → tgw-rtb-vpn → appliance-vpc-attach →gwlb endpoint/equipment [NAT translation SNAT and DNAT] src 192.168.0.0/16 dst 10.0.0.0/16 → tgw-rtb-Pilot#1 → tgw-att-Dest VPC → VPC Blue 10.0.0.0/16
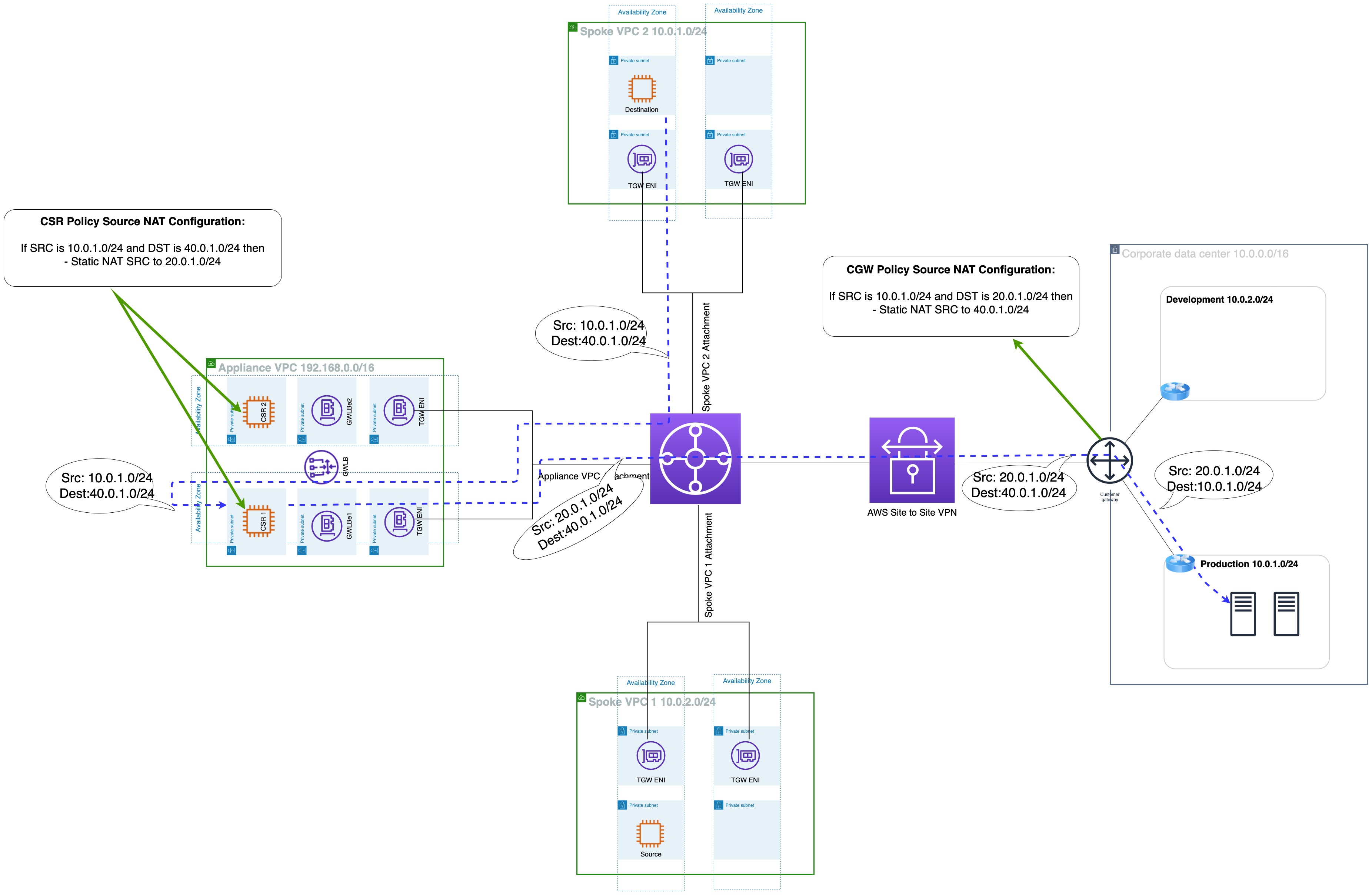
Equally, return site visitors circulation:
Dest VPC 10.0.0.0/16 → tgw-rtb-dest vpc → tgw-attach-pilot#2 → NAT occasion in pilot VPC#2 [NAT translation SNAT and DNAT] src 192.168.0.0/16 dst 10.0.0.0/16 → tgw-rtb-pilot vpc#2 → tgw-att-vpn → On-premise 10.0.0.0/16
When the on-premise host connects to the EC2 occasion in VPC, the supply IP will likely be 10.0.1.7 and the vacation spot IP will likely be 20.0.1.8. Now, the on-premise host will ship this packet to on-premise CGW, who will change the Supply IP to 40.0.1.7 in accordance with its Coverage NAT configuration. The identical will happen when the EC2 occasion connects to an on-premise host: the supply IP will likely be 10.0.1.8 and a vacation spot of 40.0.1.7. This packet will likely be despatched to the Digital router, which is able to translate the supply IP to twenty.0.1.8. Contained in the VPN tunnel, the packets will seem as if the 40.0.1.0/24 community is chatting with the 20.0.1.0/24 community.
When every host’s packet arrives on the router on the opposite aspect, the router interprets the vacation spot handle to the corresponding IP handle. The digital router will un-translate the vacation spot IP of the obtained packet from 20.0.1.8 to 10.0.1.8 and ship the packet to the EC2 occasion. Equally, the On-premise buyer gateway will un-translate the vacation spot IP of the obtained packet from 40.0.1.7 to 10.0.1.7 and ship the packet to the on-premise host. It will allow hosts in on-premise and EC2 in AWS VPN to attach to one another, regardless of each websites having IP addresses in overlapping networks.
The bi-directional site visitors circulation might be seen within the following determine:
- Essential word: As a way to efficiently implement this answer, please configure the TGW and VPC route desk accordingly.
Conclusion
In conclusion, by using Pilot VPC and Superior Twice NAT know-how over site-to-site VPN, organizations can overcome overlapping IP handle challenges, guaranteeing safe connectivity and seamless communication between on-premises networks and AWS VPCs. This strategy empowers enterprises to optimize their hybrid cloud infrastructure, guaranteeing knowledge privateness and community safety whereas embracing the transformative potential of cloud computing.
