A brand new pressure of ransomware dubbed ShrinkLocker is being utilized by cyberattackers to focus on enterprise computer systems. It exploits the Microsoft BitLocker encryption characteristic to encrypt the whole native drive and take away the restoration choices earlier than shutting down the PC. ShrinkLocker was found by cybersecurity agency Kaspersky, and analysts have noticed variants in Mexico, Indonesia and Jordan.
BitLocker has been used to stage ransomware assaults previously, however this pressure has “previously unreported features to maximise the damage of the attack,” Kaspersky stated in a press launch. ShrinkLocker is exclusive in that it could actually examine the model of a tool’s Home windows working system to make sure it allows the suitable BitLocker options, however deletes itself if it could actually’t.
Cristian Souza, incident response specialist at Kaspersky International Emergency Response Group, stated within the press launch, “What is particularly concerning about this case is that BitLocker, originally designed to mitigate the risks of data theft or exposure, has been repurposed by adversaries for malicious ends. It’s a cruel irony that a security measure has been weaponized in this way.”
Who’s susceptible to ShrinkLocker assault?
Firms in metal and vaccine manufacturing, in addition to a authorities entity, have been focused with ShrinkLocker to date. Nevertheless, Souza instructed TechRepublic there “is no evidence to believe that this group is targeting specific industries,” as victims are from completely different nations and sectors.
BitLocker is presently solely obtainable on the Professional, Enterprise, Training and Final editions of Home windows working techniques, however it is going to be included and mechanically activated in all variations with the discharge of Home windows 11 24H2 later this yr. This considerably will increase the potential scope of ShrinkLocker victims.
“Infections by ShrinkLocker can be critical if the victim does not have adequate proactive and reactive measures in place,” Souza added. “Since BitLocker is a native Windows feature, any machine with Windows Vista+ or Server 2008+ could be affected.”
How does ShrinkLocker work?
Though ShrinkLocker self-deletes after encrypting the goal, Kaspersky analysts had been in a position to uncover the way it works by learning a script left behind on a drive on a PC that was contaminated however didn’t have BitLocker configured.
Attackers would possibly deploy ShrinkLocker on a tool by exploiting unpatched vulnerabilities, stolen credentials or internet-facing providers to realize entry to servers. A consumer might also unintentionally obtain the script, for instance, by means of a hyperlink in a phishing e-mail.
“Once they have access to the target system, the attacker can try to exfiltrate information and finally execute the ransomware to encrypt the data,” Souza instructed TechRepublic.
As soon as the script is triggered, it makes use of Home windows Administration Instrumentation extensions and the Win32_OperatingSystem class to question details about the machine’s working system and area. If the machine runs on Home windows XP, 2000, 2003 or Vista, or the present area of the queried objects doesn’t match the goal, the script deletes itself.
SEE: Is there a easy technique to recuperate encrypted BitLocker drives?
Nevertheless, if the PC is utilizing Home windows 2008 or earlier, the script will transfer on to resizing its native mounted drives. It shrinks non-boot partitions by 100MB to create unallocated disk area, which is why it has been dubbed ShrinkLocker. New major partitions are created within the unallocated area, and the boot information are reinstalled so the system could be rebooted with the encrypted information by the sufferer.
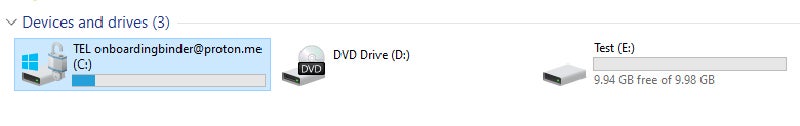
Subsequent, the script modifies Home windows registry entries to disable Distant Desktop Protocol connections and implement BitLocker settings like PIN necessities. It then renames the boot partitions with the attacker’s e-mail — onboardingbinder[at]proton[dot]me or conspiracyid9[at]protonmail[dot]com — and replaces current BitLocker key protectors to forestall restoration.
ShrinkLocker creates a brand new 64-character encryption key utilizing the random multiplication and alternative of the next parts:
- A variable with the numbers zero to 9.
- The pangram “The quick brown fox jumps over the lazy dog,” which incorporates each letter of the English alphabet, in lowercase and uppercase.
- Particular characters.
It then allows BitLocker encryption on all the machine’s drives. ShrinkLocker solely encrypts the native, mounted drive of the contaminated PC and doesn’t infect community drives doubtless to assist evade detection.
The 64-character key and a few system info are despatched to the attacker’s server by way of an HTTP POST request to a randomly generated subdomain of ‘trycloudflare[dot]com.’ It is a official area from CloudFlare that’s supposed for use by builders for testing out CloudFlare Tunnel with out including a web site to CloudFlare’s DNS. The attackers exploit it right here to cover their actual deal with.
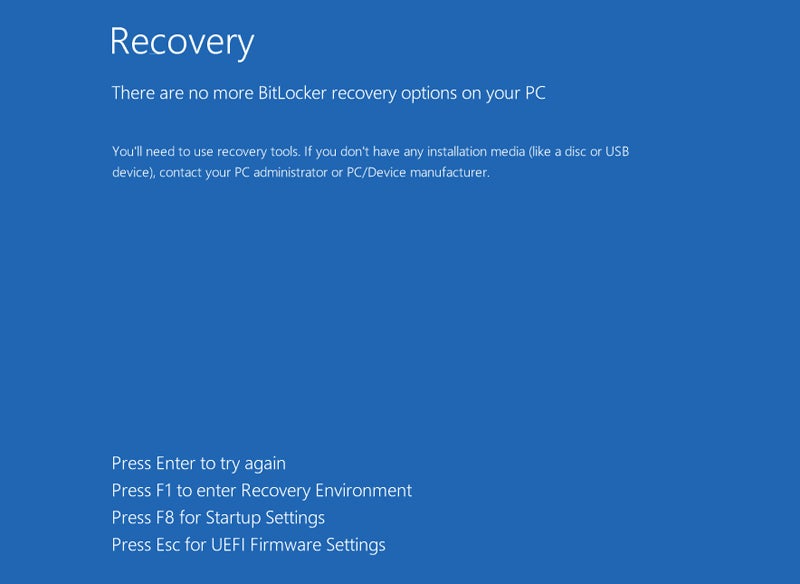
Lastly, ShrinkLocker self-deletes its script and scheduled duties, clears the logs, activates the firewall and deletes all the foundations earlier than forcing a shutdown. When the consumer reboots the machine, they’re offered with the BitLocker restoration display screen with no restoration choices obtainable — all of the PC’s knowledge is encrypted, locked and out of attain.
The brand new drive labels with the attacker’s e-mail instruct the consumer to contact them, implying a ransom demand for the decryption key.
In a technical evaluation, Kaspersky analysts describe each the detection of a ShrinkLocker assault and the decryption course of as “difficult.” The latter is especially onerous as a result of the malicious script incorporates variables which might be completely different for every affected system.
Who’s chargeable for the ShrinkLocker assaults?
Kaspersky specialists have, to date, not been in a position to determine the supply of the ShrinkLocker assaults or the place the decryption keys and different machine info are despatched. Nevertheless, some details about the attackers could be gleaned from the malware script.
The analysts stated that the script, written in VBScript, “demonstrates that the malicious actor(s) involved in this attack have an excellent understanding of Windows internals.”
The labels containing the attacker’s e-mail deal with can solely be considered if the contaminated machine is booted by an admin in a restoration surroundings or with diagnostic instruments, in line with BleepingComputer. Moreover, the BitLocker restoration display screen can have a customized observe added, but the attackers particularly selected to not create one.
The truth that the attackers seem to have deliberately made it troublesome to contact them suggests their motives are disruption and destruction quite than monetary achieve.
“For now, we know we are dealing with a very skilled group,” Souza instructed TechRepublic. “The malware we were able to analyse shows that the attackers have a deep understanding of the operating system’s internals and various living-off-the-land tools.”
How can companies shield themselves towards ShrinkLocker?
Kaspersky offers the next recommendation to companies trying to shield their units from the ShrinkLocker an infection:
- Use sturdy, correctly configured endpoint safety platforms to detect potential malicious exercise earlier than encryption.
- Implement managed detection and response to proactively scan for threats.
- Guarantee BitLocker has a powerful password and the restoration keys are saved in a safe location.
- Restrict consumer privileges to the minimal required to do their job. This fashion, no unauthorised personnel can allow encryption options or change registry keys on their very own.
- Allow community visitors logging and monitoring, capturing each GET and POST requests, as contaminated techniques might transmit passwords or keys to attacker domains.
- Monitor for VBScript and PowerShell execution occasions, saving logged scripts and instructions to an exterior repository to retain exercise even when native data are deleted.
- Make backups incessantly, retailer them offline and check them.
How has BitLocker been focused previously?
BitLocker has been focused by unhealthy actors quite a few occasions previously, properly earlier than the emergence of ShrinkLocker. In 2021, a hospital in Belgium had 40 servers and 100 TB of its knowledge encrypted after an attacker exploited BitLocker, resulting in delays in surgical procedures and the redirection of sufferers to different services.
The next yr, one other attacker focused one among Russia’s largest meat suppliers in the identical method, earlier than Microsoft reported the Iranian authorities had sponsored a variety of BitLocker-based ransomware assaults that demanded hundreds of U.S. {dollars} for the decryption key.
